OEMs face a patchwork of state biometric data privacy laws that may apply to data collected and used by new automotive technologies.
Below are 10 recently enacted or amended state-level biometric data laws that OEMs will want to be familiar with. While some of the provisions in these laws are similar, other features vary from state to state. Some of the differences that are worth noting are highlighted in this this blog post.
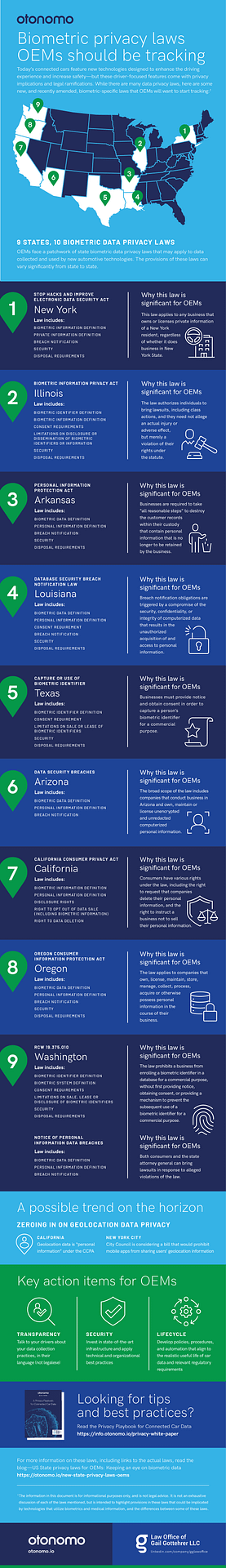
9 States, 10 Biometric Data Privacy Laws
• New York State: Stop Hacks and Improve Electronic Data Security Act (“SHIELD Act”), https://legislation.nysenate.gov/pdf/bills/2019/S5575B
• Illinois: Biometric Information Privacy Act (“BIPA”), http://www.ilga.gov/legislation/ilcs/ilcs3.asp?ActID=3004&ChapterID=57&Print=True
• Arkansas: Personal Information Protection Act, http://www.arkleg.state.ar.us/assembly/2019/2019R/Acts/Act1030.pdf
• Louisiana: Database Security Breach Notification Law, https://www.legis.la.gov/legis/ViewDocument.aspx?d=1101149
• Texas: Capture or Use of Biometric Identifier Law, https://codes.findlaw.com/tx/business-and-commerce-code/bus-com-sect-503-001.html
• Arizona: Data Security Breaches Law, https://www.azleg.gov/viewdocument/?docName=https://www.azleg.gov/ars/18/00551.htm
• California: California Consumer Privacy Act, https://leginfo.legislature.ca.gov/faces/billTextClient.xhtml?bill_id=201720180AB375
• Oregon: Oregon Consumer Information Protection Act, https://olis.leg.state.or.us/liz/2019R1/Downloads/MeasureDocument/SB684
• Washington State: RCW 19.375.010 and Notice of Personal Information Data Breaches, https://app.leg.wa.gov/RCW/default.aspx?cite=19.375,
http://lawfilesext.leg.wa.gov/biennium/2019-20/Pdf/Bills/Session%20Laws/House/1071-S.SL.pdf#page=1
See our infographic for a visual view.
Biometric Information
One variation is in the breadth of the definition of “biometric information.” The California Consumer Privacy Act (CCPA) defines it as data about an “individual’s physiological, biological or behavioral characteristics, including DNA, that can be used… to establish individual identity.” This includes “imagery of the iris, retina, fingerprint, face, hand, palm, vein patterns, and voice recordings, from which an identifier template, such as a faceprint, a minutiae template, or a voiceprint, can be extracted, and keystroke patterns or rhythms, gait patterns or rhythms, and sleep, health, or exercise data that contain identifying information.” The Illinois Biometric Information Privacy Act (BIPA) has a narrower definition of the term, defining “biometric information” as information, “based on an individual’s retina or iris scan, fingerprint, voiceprint, or scan of hand or face geometry, that is used to identify an individual.”
Personal Information
Another example is the definition of “personal information.” The Oregon Consumer Information Protection Act (Oregon Act) focuses on encryption, and defines “personal information” as (1) a consumer’s first name or first initial and last name in combination with biometric data, if encryption, redaction or other methods have not rendered the biometric data unusable or if the biometric data is encrypted and the encryption key has been acquired, or (2) biometric data without the consumer’s user name, or the consumer’s first name or first initial and last name, if encryption, redaction or other methods have not rendered the biometric data unusable and the biometric data would enable a person to commit identity theft against a consumer. By contrast, the Arizona Data Security Breaches law, makes no reference to encryption, defining “personal information” simply as an individual’s first name or first initial and last name in combination with biometric data.
Consent
Some biometrics laws, including BIPA and the Texas Capture or Use of Biometric Identifier Act (Texas Act), require companies to obtain consent to collect biometric data from individuals. Laws of other states, including the New York State Stop Hacks and Improve Electronic Data Security Act (SHIELD Act) and the Louisiana Database Security Breach Notification Law, do not have those consent requirements.
Security
The security standards imposed by these laws also vary. Texas law requires companies to use “reasonable care” to protect biometric identifiers from disclosure, and to store, transmit and secure that data in the same manner that they store, transmit, and protect other confidential information they possess, or in a more protective manner. The SHIELD Act provides a more detailed security framework, requiring covered entities to develop, implement and maintain reasonable safeguards to protect the security, confidentiality and integrity of the data, which includes a data security program that has reasonable administrative, technical, and physical safeguards. The SHIELD Act lists examples of policies and practices that constitute reasonable administrative, technical and physical safeguards.
Breach Notification
The types of security incidents that trigger notification obligations also differ across the states. For example, the Arizona Data Security Breaches law defines a “security incident” as an event that creates “reasonable suspicion” that a company’s information systems or computerized data may have been compromised or that measures put in place to protect those systems or data may have failed. The Oregon Act uses a different standard for what constitutes a security breach, defining it as an unauthorized acquisition of computerized data that “materially compromises” the security, confidentiality or integrity of personal information that a company maintains or possesses.
Disposal Requirements
Finally, while the majority of the laws discussed in the infographic mandate the disposal and destruction of biometric data, they set different deadlines. BIPA, for example, requires the disposal of an individual’s biometric data when the initial purpose for collecting or obtaining that data has been satisfied or within 3 years of the individual’s last interaction with the company, whichever occurs first. The Texas Act requires biometric data to be destroyed within a reasonable time, but not later than 1 year after the date on which the purpose for collecting the data expires. The Oregon Act sets a timeframe that is more vague, requiring biometric data to be disposed of once the business no longer needs that information for business purposes or as required by law.
Takeaway for OEMs
While calls for a federal data privacy law continue, the focus on the protection of biometric data increases. Several states have already introduced new biometric data privacy laws this year. OEMs will want to monitor the distinctive features of the existing and pending biometric data laws, which can impact their compliance obligations and potential liabilities.
About Gail Gottehrer
Gail Gottehrer is the Founder of the Law Office of Gail Gottehrer LLC in Stamford, CT. Her practice focuses on emerging technologies, including autonomous vehicles, AI, biometrics, robots and facial recognition technology, and the privacy and security laws and ethical issues associated with the data collected and used by these technologies. She is one of the few defense lawyers to have been involved in the trial of a class action to verdict before a jury. Gail teaches Law for Knowledge Innovation at Columbia University, and is a member of the State of Connecticut’s Task Force to Study Fully Autonomous Vehicles and the New York State Bar Association’s Task Force on Autonomous Vehicles and the Law. She is also a member of the ITU’s Focus Group on AI for Autonomous and Assisted Driving. Her recent publications include Can States Steer Clear of Liability for Accidents Involving Autonomous Vehicle Technology?, an article published by the American Bar Association.
1 The information in this document is for informational purposes only, and is not legal advice.







